Effective collaboration between teams that exchange data depends as much on clearly defined governance as it does on robust engineering. When multiple teams produce and consume data, interfaces evolve, expectations diverge, and incidental breakages can ripple across services. Versioning and validation are the twin practices that keep these interfaces stable, predictable, and safe to evolve. They reduce coordination overhead, increase deployment velocity, and protect consumers from unexpected regressions.
The role of formal agreements
A practical approach begins with explicit agreements on the shape and semantics of exchanged data. These agreements should be discoverable and enforceable so that both providers and consumers can rely on a single source of truth. For example, one way teams codify expectations is by maintaining formal schema definitions and contract tests in a shared registry. In many organizations this takes the form of data contracts that are versioned alongside code and schemas, making changes auditable and testable.
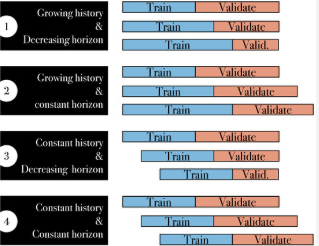
Versioning strategies that work
Choosing a versioning strategy is a strategic decision. Semantic versioning principles provide a useful shorthand: patch for backward-compatible fixes, minor for additive, and major for breaking changes. However, apply these principles pragmatically rather than dogmatically. For some large-scale event streams or pub/sub topics, adding optional fields is a minor change only if consumers ignore unknown fields by default; otherwise, it becomes a breaking change. In RPC-style systems, evolving method signatures generally requires stricter controls. A robust strategy includes clear rules for compatible changes, deprecation timelines, and how major versions are published and discovered. Consumers should be able to bind to a stable major version while providers iterate within minor and patch releases.
Automated validation as the gatekeeper
Automated validation is the most effective way to prevent breakages from reaching production. Validation operates at multiple layers: schema validation at runtime or ingress, contract tests in CI, and integration tests that exercise live endpoints. Schema validators enforce structural correctness, ensuring that required fields exist and that types match expectations. Contract tests compare provider behavior against the agreed specification, while integration tests validate the interaction in realistic conditions. Combined, these checks create a safety net that catches both syntactic and semantic regressions before they impact downstream teams.
Consumer-driven testing and registration
When interfaces are shared across teams, expect consumers to have diverse needs. Consumer-driven testing flips ownership of some tests to the downstream teams so that providers run tests expressing consumer expectations. These tests form part of the contract verification suite and are crucial for catching edge cases that provider teams might not anticipate. A registration system that records consumer-test dependencies provides visibility into which consumers depend on which parts of an interface. When a provider proposes a change, the registry should trigger automated tests for all dependent consumers, surfacing potential breakages early in the change lifecycle.
Compatibility policies and deprecation
No interface lives forever in the same form, so having a clear deprecation policy is essential. Define what constitutes a breaking change and how long deprecated features remain supported. Communicate timelines and migration guides proactively so consumers can plan. Implement compatibility checks in CI that enforce the policy: pull requests that remove fields, change types, or alter semantics should be blocked until a migration plan is submitted and consumer tests pass. For complex migrations, provide feature flags or dual-write strategies that allow providers and consumers to transition incrementally without global coordination.
Observability and runtime checks
Even with rigorous testing, production anomalies happen. Observability tools that track schema violations, unexpected nulls, or significant shifts in field cardinality enable teams to detect and diagnose issues quickly. Instrumented endpoints should emit metrics when incoming messages fail schema validation or when contract expectations are not met. These metrics feed into alerts and dashboards so engineers can prioritize fixes based on consumer impact. Runbooks that map common validation errors to remediation steps speed incident resolution and reduce finger-pointing between teams.
Tooling and infrastructure considerations
Investing in toolchains that integrate schema registries, contract testing frameworks, and CI validation yields long-term dividends. A central schema registry with version history and compatibility checks helps prevent accidental incompatible changes. Contract testing frameworks that can be executed in CI pipelines and the ability to publish test results to a shared dashboard make the change process transparent. Additionally, ensuring that your CI/CD tooling supports environment-specific validation—so that contracts are verified against staging endpoints as well as mock implementations—helps surface integration issues earlier.
Organizational practices to support technical controls
Technical safeguards alone are insufficient without cultural and process disciplines. Establishing clear ownership for interfaces, defining change approval workflows, and creating cross-team change windows for high-impact migrations reduce friction. Encourage API design reviews that include providers and major consumers so semantic changes are debated and documented before implementation. Regularly scheduled compatibility audits and post-mortems for incidents involving interface changes cultivate institutional knowledge and continuous improvement.
Making evolution predictable
Versioning and validation should make evolution a predictable, low-risk activity rather than a source of anxiety. When teams treat interface changes as first-class artifacts—versioned, tested, and observable—they gain the freedom to innovate while keeping downstream systems safe. The goal is not to eliminate change but to institutionalize change in a way that is transparent, reversible, and minimally disruptive. With clear policies, automated validation, and a culture that values cross-team collaboration, interfaces become reliable conduits of functionality rather than brittle points of failure.
Final perspective
Cross-team data interfaces are the lifeblood of modern distributed systems, and their healthy evolution depends on disciplined versioning and validation practices. By combining formal agreements, rigorous testing strategies, operational visibility, and organizational processes, teams can confidently evolve interfaces without repeatedly paying the cost of coordination or incident recovery. The payoff is faster delivery, fewer outages, and stronger alignment between those who produce data and those who consume it.